In today’s digital landscape, identity-based security is now key. In the past, security was primarily focused on securing the network perimeter, keeping the cyber criminals out of the corporate network, because most employees worked from a physical office behind a corporate firewall. However, remote working, the use of cloud computing, mobile devices (corporate and personal) accessing company data, and the Internet of Things (IoT) are now common place, meaning the traditional approach to security is no longer sufficient. This has resulted in the rise of identity-based security.
What is identity-based security?
Identity-based security focuses on individual users and their credentials, rather than the network perimeter, to solve the problem of enabling a secure way for employees and customers to access company resources from anywhere, using any device. Usernames and passwords are usually used for authentication, but these do not offer an appropriate level of identity security. According to Verizon’s 2022 Data Breach Investigations Report, password security issues accounts for over 80% of all data breaches globally. Hence, multi-factor authentication (MFA) is used alongside passwords to offer a stronger means of authentication, reducing the chances of credential compromise, we recommend every organisation should have MFA enabled wherever possible.
There are different types of MFA, such as SMS MFA, Authenticator apps, biometric authentication, hardware token and physical keys. Not all of these MFA options are created equal. The SMS-based multi-factor authentication (SMS-MFA) is a widely used security measure that requires users to enter a code sent via text message in addition to their password. However, SMS MFA is not without its vulnerabilities, the most significant risks is the Intercept attack. In this blog post, we will discuss these forms of attack in more detail.
What is an SMS intercept attack?
An SMS-MFA intercept attack is a type of cyber-attack where a hacker intercepts the SMS code sent to a user’s phone number during the MFA process and uses this to gain access to their account. This is usually done by tricking the mobile network into redirecting the SMS message to a device controlled by the attacker.
To carry out this attack, the hacker first needs to know the victim’s phone number and the website or service they are attempting to access. They then initiate a login request, triggering the MFA process, and wait for the SMS code to be sent. The hacker then redirects the SMS code to their own device, allowing them to enter the code and gain access to the victim’s account.
A SMS MFA intercept attack with a man-in-the-middle (MITM), is another type of attack that occurs when a cybercriminal sits between the victim and target website and intercepts the code sent to the user’s phone when an MFA request is made, using it to gain access to their account. In this type of attack all communications between the victim and target website is routed via the MITM.

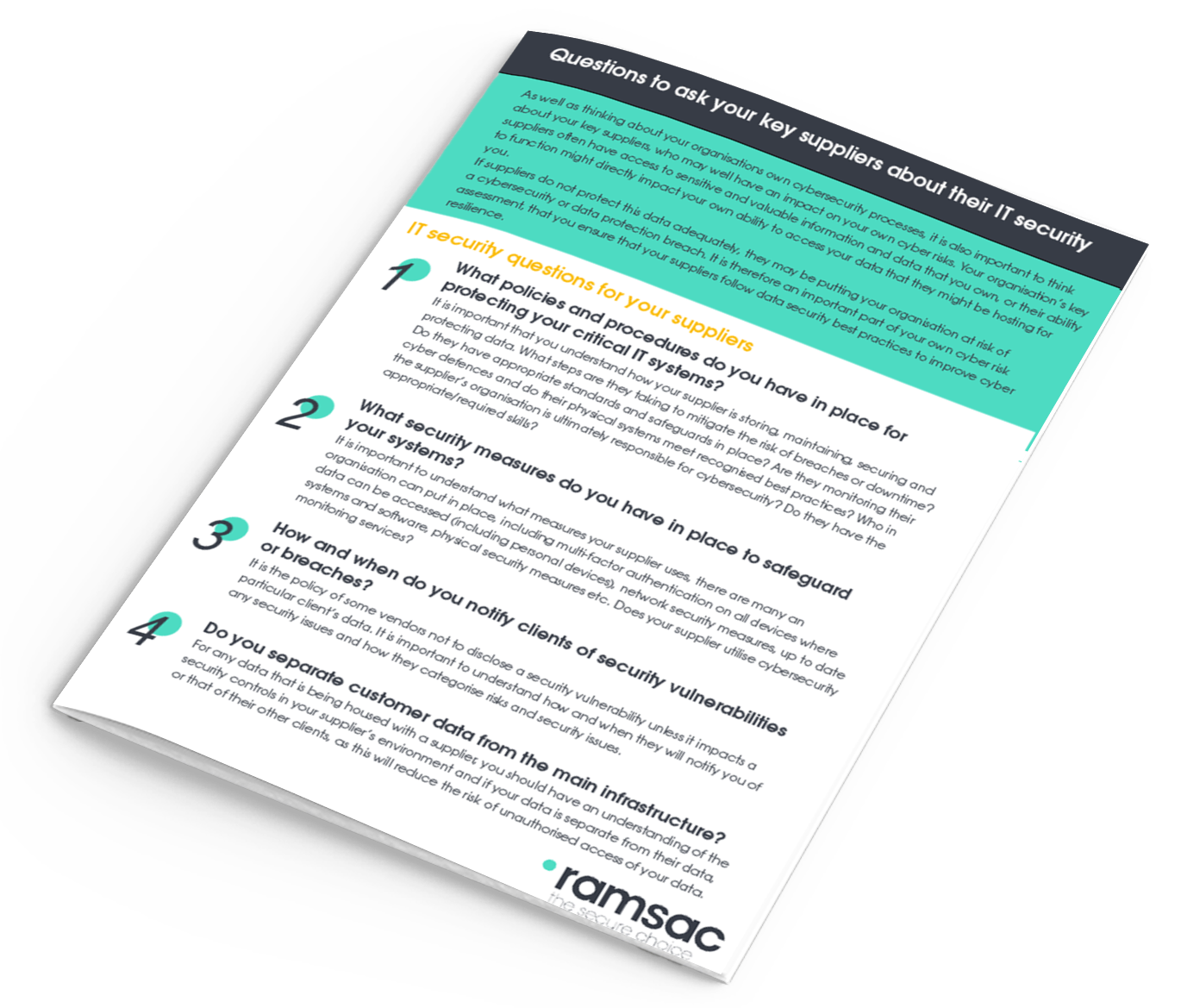
IT Security Questions for Key Suppliers
Why is SMS MFA intercept attack a threat?
SMS MFA intercept attacks pose a significant threat because they can bypass the additional layer of security provided by MFA. While SMS MFA is still more secure than a simple password, it is still vulnerable to attacks because it relies on the security of the mobile network, which can be compromised. Hence, the security issue is not with MFA, but with transmission of the of the code, which is done in the clear for both SMS and voice calls, making it susceptible to interception by a determined attacker.
Hackers can use a variety of techniques to intercept SMS messages, including SIM swapping, where they trick the mobile network into transferring the victim’s phone number to a device controlled by the attacker, and SS7 attacks, where they exploit vulnerabilities in the signalling system used by mobile networks to redirect SMS messages.
How do we defend against these MFA intercept attacks
Although MFA using SMS offers more protection than passwords, users can still be compromised in some instances. SMS and voice MFA seem to offer the lowest level of security compared to other forms of MFA such as authentication apps, biometrics, hard tokens and physical keys.
Microsoft recommends the use of the authenticator apps on mobile phones as the minimum for MFA. The authenticator app can be configured for passwordless sign in using biometric authentication to provide further security. This will defend against some of the SMS MFA interception attacks reliant on mobile networks discussed earlier. However, a victim using the MFA authenticator app could still be vulnerable to a man in the middle proxy interception attack because all communication between the victim and target website passes through the attacker’s server.
Our recommendations for protecting against these types of attacks are:
- Deploy an advanced email security and resilience tool that can block phishing attacks.
- Remind all users not to visit untrusted websites or follow links/open files provided by unknown or untrusted sources.
- Train employees to recognise social engineering attacks such as phishing.
- Establish and maintain an ongoing security awareness program.
- Use behavioural based security monitoring tools such as SIEM/SOAR tools that can spot any anomaly in a user identity behaviour.
Contact us to understand steps you can take to protect against these man in the middle attacks and how to improve the cyber resilience of your organisation.

Worried about your IT security?
Speak to us today about your cybersecurity concerns.










