Every organisation is at risk of cybercrime. Hackers are developing increasingly sophisticated ways to access information, regardless of the type of data it is, and protecting it has become a top priority for all businesses large and small. According to the latest UK Government figures, 32% of all businesses and 24% of charities experienced a data breach over a 12-month period.
A cyberattack involving data loss or the disclosure of sensitive information can be devastating for any business. From damage to reputation to serious financial penalties, there are severe consequences for companies that allow sensitive data to get into the wrong hands.
To protect your business from data theft, you’ll first have to understand what sensitive data looks like within your organisation. This blog will provide a selection of sensitive data examples to help you identify any vulnerabilities within your business’s digital security system.
Sensitive data examples within an organisation

Any confidential information that’s stored, processed, or managed by an individual or organisation can be classified as sensitive data. Information is labelled ‘sensitive’ because of the damage that would be caused if it fell into the hands of cybercriminals. There are many forms of sensitive data within an organisation, and examples include personal, financial, and business information relating to clients, employees, suppliers, and more. Hackers attempt to steal this data to commit fraud, identity theft, and other illegal cybercrimes. An in-depth cybersecurity audit can help you identify this.
All organisations must protect their sensitive data against unauthorised access and mitigate the risks of cybercrime. Four common examples of sensitive data within a business include:
1. Personal information
Personal information, also known as personally identifiable information (PII), is data that can be used to identify or verify a person or organisation. This may include someone’s home address, phone number, and date of birth.
Personal data can be either sensitive or non-sensitive because details like names and phone numbers can easily be found in public records, and cybercriminals are unlikely to cause harm when armed with this information alone. However, sensitive personal information can relate to passport numbers, driver’s licence numbers, medical records, and other data that could lead to identity theft, and therefore must be protected by any organisation that stores these confidential details. PII includes :
| Sensitive Personally Identifiable Information (PII) | Non-sensitive Personally Identifiable Information (PII) |
| Bank account and credit card details | Full name |
| Passport number | Email address |
| Driving licence | Mobile phone number |
| National Insurance number | Home address |
| Medical insurance details | Social media profile |
2. Business data
Sensitive data such as intellectual property, trade secrets, accounting information, and confidential customer and supplier information that could seriously damage a business if stolen or disclosed.
3. Financial data
This includes any financial data related to a person or to the business, such as bank and credit card details, National Insurance numbers, tax filings, and other social security information.
4. Credential details
Details such as usernames, passwords, and personal identification numbers that are used to access a system, app, device, or even information stored on key fobs that allow entry into a premises as well as biometric data held on facial or fingerprint recognition apps.

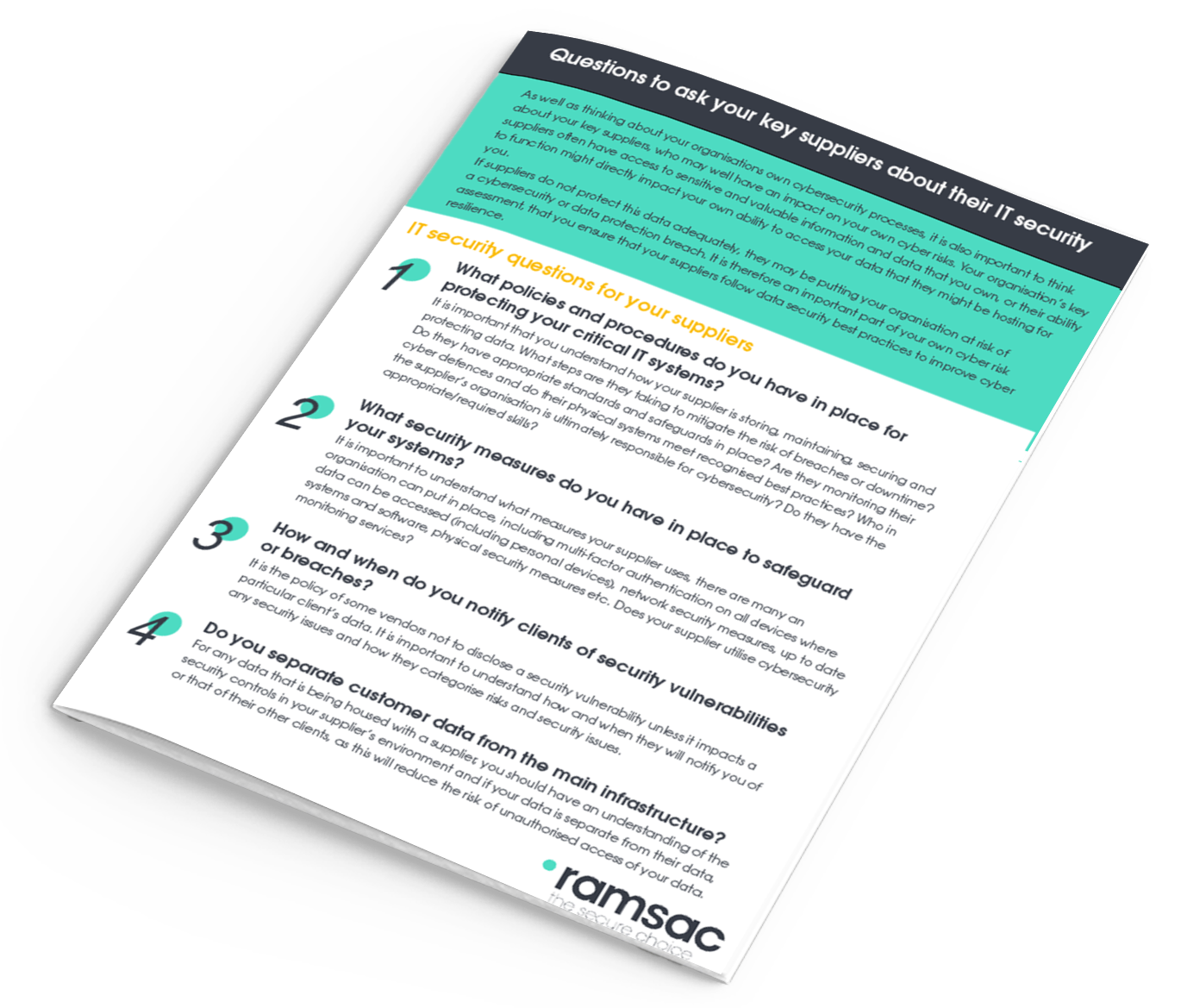
IT Security Questions for Key Suppliers
Why would cybercriminals want this data?
There are many reasons why cybercriminals look to exploit weaknesses in company systems to gain access to their sensitive data. For example, hackers could use a combination of personal information and financial data to steal a user’s identity for the purpose of committing fraud.
Companies that fail to protect their sensitive data may suffer financial loss, costly penalties, and reputational damage as a result of a cyberattack. However, with the right tools, cybersecurity software, and expertise, businesses can protect their sensitive data and avoid the dire consequences associated with a cyberattack.

What regulations are there around sensitive data within an organisation?
Strict government and industry regulations exist to enforce data protection for the public and provide clear guidelines around the collection of PII and how it should be used. If your business handles sensitive data, here are some examples of the regulations currently in place:
The Data Protection Act
In the UK, the Data Protection Act 2018 dictates how sensitive and personal information is used by organisations, businesses, or the government. It is part of the UK’s implementation of the General Data Protection Regulation (GDPR).
The Data Protection Act includes strict rules for any group that handles personal data so that sensitive information is used fairly, lawfully, and transparently, and for specified and explicit purposes only. The Act is designed to ensure organisations adopt the appropriate security measures to protect their data from the threat of a cyberattack.
General Data Protection Regulation (GDPR)
The General Data Protection Regulation is a detailed data privacy law active in the European Union, UK and European Economic Area. There is the EU GPDR and the UK GDPR, which was put into place after Brexit. EU GDPR no longer applies to the UK, and businesses that operate inside the UK.
The UK version protects the personal data of individuals and determines how this sensitive information may be used, stored, processed, managed, and protected by an organisation that either operates in the area, or processes the data of individuals within the EU.
While GDPR rules can be complicated, they are designed to safeguard sensitive data and prevent unauthorised access, with significant fines and penalties in place for violating the regulations.
Other Global Sensitive Data Regulations
Many countries have introduced their own data protection regulations. For example, the California Consumer Privacy Act (CCPA) is a data privacy law aimed at protecting consumer rights by obliging businesses to inform customers how they handle their data.
The United States has also introduced the Health Insurance Portability and Accountability Act (HIPAA) that sets privacy standards for protecting sensitive patient information and medical records.
Meanwhile, the Payment Card Industry Data Security Standard (PCI DSS) is made up of a set of policies, procedures, and tools for protecting a cardholder’s data. The aim is to create a secure and accountable environment that protects both consumers and businesses from security breaches and card data theft.
The regulations mentioned in this blog, along with laws surrounding PII, are often updated, and businesses are urged to research the regulations that affect them directly around sensitive data, and how personal information is stored and processed.
What do organisations need to do to protect their data?
Organisations and businesses can protect their data in many ways and reduce the risk of a cyber attack or data breach. From encrypting data to training employees to be a human firewall, there are several effective measures that users can adopt to help keep sensitive data safe. These include:
Train employees to be a human firewall
Cybersecurity training is one of the most effective ways to strengthen your organisation’s security and improve its resilience against cyber criminals. With proper training in cybersecurity and phishing awareness, your employees can form a robust human firewall that will ensure data is fully protected against increasingly sophisticated threats.
Put permission levels in place
The rise in remote and hybrid working places new challenges on organisations when it comes to managing multiple devices that access company resources and systems. Therefore, leaders are constantly looking for the most reliable solutions for protecting company data, managing user access, and supporting employees who work from afar. Endpoint management solutions including cloud-based Software such as Microsoft Intune allows you to take control of user access and simplify the supervision of devices including desktop computers, laptops, and smartphones.
Monitor for potential data breaches
Cybercriminals work around the clock, so your cybersecurity defences need to operate 24/7 to keep up with the constant threat of attack. Cybersecurity monitoring allows organisations to continuously scan for potential threats and breaches so your data is always protected. Not only can monitoring detect a breach immediately, but it also enables you to take action, prevent further impact, and limit any long-term damage.
Do you need help with protecting your sensitive data?
It has never been more important to ensure your IT systems are secure, and your sensitive data is protected from cybercriminals. At ramsac, we provide a range of cybersecurity solutions such as 24/7 cybersecurity monitoring and employee training that safeguard your organisation from cyber attacks. Before you suffer a data breach, contact us today.










