Worldwide spending on cybersecurity technologies $71.1 billion. But the most secure cybersecurity systems can be undone by a Post-it note. That’s why every business needs a secure human firewall.
What is a human firewall?
A human firewall is a collective group of people who actively work to prevent cyberattacks, data breaches or suspicious activity, often within a business. A human firewall should always be a core part of any organisation’s cybersecurity strategy.
In an age where AI cybersecurity threats are more potent than ever, it’s essential that your human firewall is strong and robust. While a human firewall is our biggest line of defence against cybercrime, it is also our biggest risk. It’s all too easy for users to accidentally drop their guard, or unintentionally click on a bad link in an email.
Here’s an easy example of your human firewall. It’s that part of you that says “This is too good to be true,” when a mysterious millionaire emails out of the blue and wants to send you money via bank transfer. That’s an old scam, but it still works. And today, cybercriminals are devising subtler ways to breach our human firewall.
How does a human firewall work?
A human firewall works by querying and challenging any suspicious activity that you come across. For example, you receive an email from your boss asking you to buy a selection of gift cards. However, before you take any action or make any purchase, you decide it is better to confirm with your boss that they sent the email requesting you buy gift cards, not a cybercriminal.
Or, if you get a message asking for bank details to confirm a payment, you check who has sent the email and ensure it’s the email address you expect.
All of these checks that a computer can’t do for us make up the human firewall. To create a human firewall, people need regular training and awareness, as well as up-to-date information on the latest threats. When employees receive the appropriate training to strengthen the human firewall, they will better protect your IT network from extremely damaging cyberattacks.
Why is a human firewall important?
A human firewall is important because everyone who has access to your systems is also a potential vulnerability. And we aren’t just talking people who aren’t “digital natives”. Cybersecurity is a numbers game. Criminals only need the tiniest bit of information to do extraordinary things. While cybersecurity software can protect your systems, humans aren’t as good at spotting threats. Because we’re just that: human.
Everyone thinks they’re safe and secure online. We trust the coffee shop Wi-Fi. We see no harm in liking the Facebook page. But as you’ll see in the video below, safety is not guaranteed…
Why is a human firewall an essential part of a cybersecurity strategy?
A human firewall is an essential part of your cybersecurity strategy. You could have all the best tools, but if no one is using them, what’s the point of having them?
For example, if you had CCTV around your house but left the door unlocked, what’s the point of the CCTV? The same applies to cybersecurity, you could have the right equipment to secure your IT estate, but human error could let a malicious actor slip right in.
How does a cyber breach affect your business?
The average cost of a cybersecurity breach to a business is expansive. You don’t only have to consider the material cost and potential fines, but long-term factors, too.
According to Deloitte, 30% of consumers said they would stop dealing with a business hit by cybersecurity breach, even if they don’t suffer personally. According to Aviva, after you suffer a breach, 60% of your customers will think about moving, and 30% actually do.
Ultimately, a cybersecurity breach will almost certainly have a negative impact on company profit given the estimated cost. That, in turn, could be extremely detrimental to a number of other financial factors including share price which could lead to a loss of confidence from stakeholders and investors.
How to improve your human firewall
One person alone cannot secure the human firewall. It requires everyone in the business to maintain awareness and security.
You can improve your human firewall through:
- regular training
- cybersecurity updates against the latest kinds of breaches
- a clear way to report suspected incidents
More often than not, your staff are victims of cybercrime. 25% of staff who cause breaches are inadvertent actors. You can protect them by only allowing access to information on a “need-to-know” basis. If a company of 100 employees only grants personal data to a payroll team of 3, hackers will have a much harder time accessing that information.

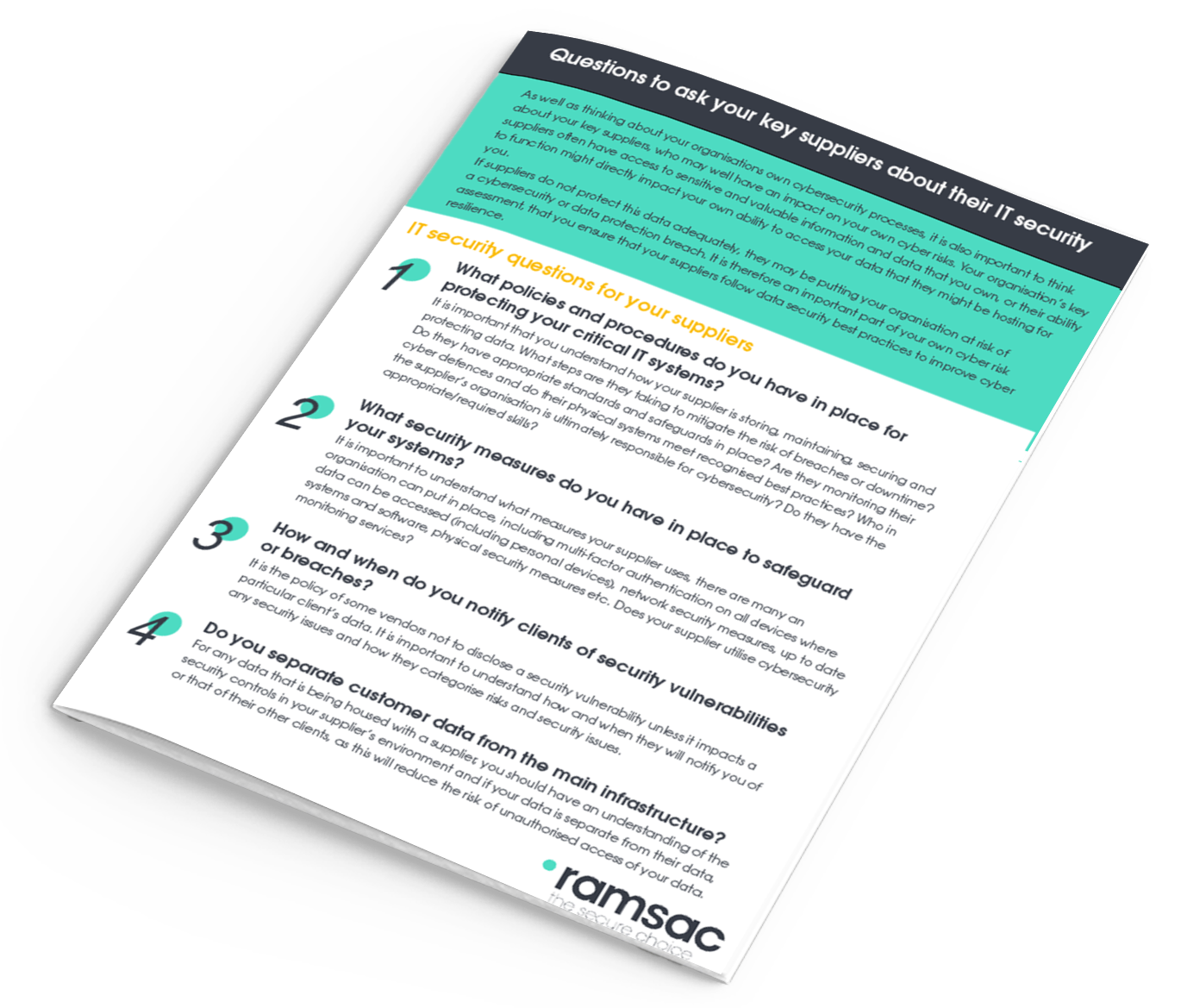
IT Security Questions for Key Suppliers
The benefits and limitations of cybersecurity training
Many organisations and individuals have fallen foul of ‘phishing’ or ‘whaling’ scams. All of these could have been prevented if the right training and knowledge was in place.
All organisations should be spending the equivalent of between 30-60% of their IT budget on staff training. A good proportion of that should go towards cybersecurity.
Despite this, only 1 in 5 businesses in the UK carry out any form of cyber training. If you ask them about that training, they’ll likely tell you that there’s a policy document, or there’s something about it in the employee handbook.
In order for someone to “know” something, they need to be told about six times. For larger organisations, 50-minute refresher training every 6 months is not enough to keep staff trained on cybersecurity.
However, training is very important. CEOs and other senior managers are especially in need of training for two reasons:
- They are the people who are least likely to have taken training in the past
- They are most likely to be the targets of cybercrime
40% of senior managers in a BAE Systems survey said they lack understanding of their own company’s cybersecurity protocols. But if you’re the boss, you’re an attractive target for cyber criminals as you’re more likely to have access to funds and resources that are more valuable for a cybercriminal.
That’s why ramsac run in-depth training courses in cybersecurity to help business leaders stay up-to-date and informed about the latest cyber risks.
How to be a human firewall
Being the human firewall means making the right judgement every time you receive an email or decide to connect to a network.
We need to create a culture that is curious and cautious. A culture that rewards people who take the time to pick up the phone and double check with the CEO that the email they sent really was from them.
People need to have accountability if they’re the ones in the hot seat. But, they need to trust that it’s okay to turn to the most senior person in the business and confirm their orders.
It’s all too easy for staff to pass the buck up the line, especially if requests for assurance are interpreted as belligerence or interfering. In this way, creating a more open office culture can help protect you from cyberattacks.
Challenge your staff to question the norms. It doesn’t just help protect your business. It creates a workplace of innovation and ideas.
Cybersecurity is not an IT problem
Cybersecurity affects everyone, not just in our professional lives, but in our personal lives too. It’s everyone’s responsibility to stay aware of emerging threats and be mindful of danger every day.
Cybercrime is evolving and companies are being exposed to new scams all the time. When we build a culture that’s mindful of cybersecurity, we can protect ourselves and our businesses more effectively.
ramsac can help you change the way your business thinks about cybersecurity. Our new Cyber Resilience Certification tests how ready you are for a cyberattack, and provides you with a grade depending on your competence. For cyber protection and peace of mind, contact ramsac now.










